Welcome to the EPSRC Centre for Doctoral Training (CDT) in Cyber Security for the Everyday at Royal Holloway.



Follow us on our social media platforms to keep up to date with CDT news and activities
The Centre was first established in 2013, and has as its main objective to develop cohorts of multidisciplinary researchers with a broad understanding of cyber security and a strong appreciation of the interplay between technical and social issues.
Research in the CDT will address challenges concerning:
- the technologies deployed in digital systems that people use, sometimes inadvertently, every day.
- the everyday societal experience and practice of security.
The CDT is centred around Royal Holloway's Information Security Group and partners with departments throughout the institution. CDT researchers follow a four-year PhD programme. The first year consists of comprehensive multidisciplinary cyber security training. The remaining three years focus on research in an advanced topic in the field of cyber security.
In each annual cohort, we award approximately ten fully-funded PhD studentships (four years of enhanced stipend and fees). We welcome applications from candidates with undergraduate and/or masters qualifications in a wide range of technical and social disciplines of relevance to cyber security.
The CDT is not currently accepting applications for UKRI funded PhD studentships
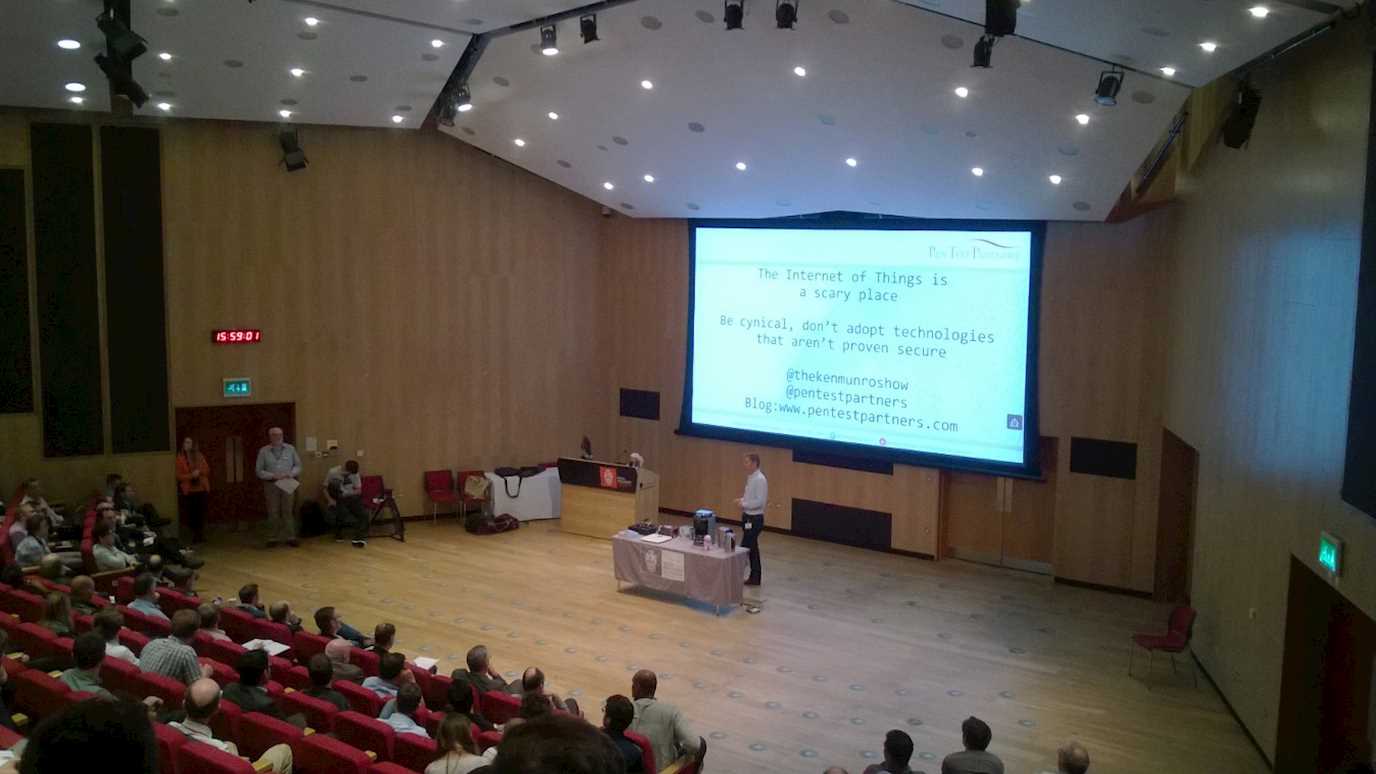
Sample Research Topics
Our research topics take advantage of the CDT's interdisciplinary nature to tackle major challenges in many different areas of cyber security. These are not the only topics we supervise, but they do demonstrate the range of research areas we cover.
A list of sample research topics can be found here
Management and Governence
Director
Prof Keith Martin is the CDT Director and is responsible for the day-to-day management of the CDT. Responsibilities include coordinating recruitment, overseeing delivery of training, arrangement and management of supervision and liaison with external partners. The CDT Director also acts as the ultimate point of contact for CDT student welfare issues.
Manager
Harpreet Sanghera-Dhanjal is the CDT Manager, supporting day-to-day running of the CDT and acting as a first point of contact for CDT students, with particular responsibilities for managing admissions, financial reporting, communications and event management.
Management Committee
The Management Committee is chaired by the CDT Director, and supports all aspects of the CDT operation. The Management Committee is:
Professor Peter Adey
Dr Michelle Bentley
Professor Lizzie Coles-Kemp
Dr Rikke Jensen (Deputy Director)
Dr Dan O'Keeffe
Dr Rachel Player
Advisory Panel
The Advisory Panel provides independent advice on the strategic direction, coverage and progress of the CDT. The Advisory Panel includes experts from industry, academia and public sector. The Advisory Panel is:
Timothy Bauge Research Group Leader: Thales UK
Bedria Bedri Deloitte
Robert Carolina Internet Systems Consortium
Dr Sepi Chakaveh CEO/Founder Pixsellar
Professor Liqun Chen University of Surrey
Budgie Dhanda MBE 3BDA
Professor Paul Dorey (Advisory Panel Chair) CSO Confidential. IISP
Irfan Hemini DCMS
Dr Richard Horne PwC
Professor Johannes Kinder LMU, Munich
Emma Leith Bridewell
Peter Lockhart Roke Manor Research
Shilon Bala EPSRC - Digital Security & Resilience
Professor Igor Muttik CEO: Cyber Curio
Professor Kenny Paterson ETH Zurich
Professor Bart Preneel KU Leuven
Dr Simon Shiu HP Labs
Dr Thyla van der Merwe Google
Publications
The CDT publications list highlights the work undertaken by our staff and students. The full list of published articles can be found here